TraceLock™ — Multi-Domain RF Threat Detection Platform¶
WGU BSCSIA Capstone · Degree Conferred March 2026
Role: Sole developer | Security-hardened fork | ~12,500 LOC (25 Python modules, 81 shell scripts) | 6 RF domains
For Hiring Managers — Detection Engineer / Security Automation
What I Built: Real-time RF surveillance detection system that monitors 6 wireless domains simultaneously, correlates threats across sensors, and produces forensic-grade evidence logs.
Technical Stack: Python 3.10+ · ARM SBC · RF Monitoring Framework · SDR Receivers · BLE Adapters · SQLite · GitHub Actions CI
Detection Engineering Skills Demonstrated:
- Multi-domain threat correlation (Wi-Fi + Bluetooth + SDR + GPS + ADS-B)
- Custom detection rule authoring with tunable thresholds
- False positive reduction through AI-assisted pattern extraction
- Real-time alerting with structured logging pipelines
- Security hardening (parameterized queries, encrypted credentials, input validation)
Why This Matters: If I can build detection logic for RF threats across 6 sensor domains, I can build detection content for your SIEM/EDR platform.
View TraceLock Public Public Artifacts
Case summary¶
| Problem | Security teams face 12–18 minute RF blind spots during sweep operations; existing tools monitor single wireless domains with no cross-domain correlation |
| Environment | Raspberry Pi 4 (8GB) · Python 3.10+ · RF Monitoring Framework · RTL-SDR V4 · Ubertooth · SQLite · GitHub Actions CI |
| What I built | Real-time multi-domain sensor fusion: Wi-Fi + BLE + SDR + GPS + ADS-B correlation engine with forensic-grade logging and tunable detection thresholds |
| Framework mapping | Detection engineering fundamentals · evidence-grade logging aligned with audit trail requirements · MITRE ATT&CK for ICS (RF threat vectors) |
| Measurable outcome | Eliminates RF blind spots across 6 simultaneous domains; patent-pending architecture; WGU BSCSIA capstone (Mar 2026) |
| Artifacts | Public repo · ~12,500 LOC · 25 Python modules · 81 shell scripts · example detection outputs |
Governed Agentic Security Stack — Agentic Detection & Adversarial Validation Layer
Stack Position: TraceLock™ is the Agentic Detection & Adversarial Validation Layer of the Governed Agentic Security Stack — the layer that detects adversarial signals in the environment where AI-governed security workflows operate.
Architectural Risk Reduced: RF-layer blind spots that leave security operations without environmental threat visibility. A GRC platform that automates compliance workflows is only defensible if the physical environment it operates within is actively monitored.
Stack Layer: Agentic Detection (primary) · Adversarial Validation (secondary) · Evidence & Assurance (cross-layer) | Governed Agentic Security Stack
Relationship to GIAP™: GIAP™ governs compliance intake workflows. TraceLock™ monitors the physical RF environment those workflows operate within. Without detection coverage at this layer, GIAP™'s audit trails lack environmental context — a session conducted during active RF surveillance leaves no record of that condition.
The Problem¶
Executive protection and security teams face a critical gap: 12-18 minutes of RF blind spots during sweep operations. Existing tools monitor single domains (Wi-Fi OR Bluetooth OR SDR) without correlation, missing sophisticated threats that hop frequencies or use multiple channels.
Attack scenarios addressed:
- Rogue Wi-Fi access points for credential harvesting
- Bluetooth tracking devices (AirTags, Tiles, custom beacons)
- ISM-band triggers for remote activation
- GPS spoofing and jamming detection
- Unauthorized drone surveillance (ADS-B correlation)
TraceLock vs. Traditional Wireless IDS¶
| Capability | Traditional WIDS | TraceLock™ |
|---|---|---|
| Domains monitored | Wi-Fi only | 6 domains (Wi-Fi, BLE, SDR, GPS, ADS-B, cellular) |
| Detection approach | Signature-based | Multi-domain correlation with behavioral analysis |
| Evidence grade | Alert logs only | Forensic-grade structured logging with chain of custody |
| Hardware | Enterprise appliances ($10K+) | Raspberry Pi + commodity SDR (~$200) |
| Deployment | Fixed infrastructure | Portable, field-deployable |
| Governance | None | SDOS-governed decision pipeline |
Use Cases & Transferable Skills¶
| Scenario | Domain | Skills Demonstrated |
|---|---|---|
| Executive Protection | Physical Security | Surveillance detection, persistence scoring, threat correlation |
| Detection Engineering | SOC/SIEM | Multi-source correlation, threshold tuning, false positive reduction |
| Forensic Evidence | Legal/GRC | Audit-grade logging, KML visualization, chain of custody |
| Drone Surveillance | AAM/Critical Infrastructure | ADS-B decoding, airspace monitoring, RF signal analysis |
TraceLock™ addresses 25+ documented scenarios — from border security to disaster response. The same detection logic applies to any domain requiring multi-sensor correlation.
What I Built Beyond the Original¶
TraceLock™ is a security-hardened fork of CYT (Chasing Your Tail). Here's what I added:
| Component | Original CYT | TraceLock™ (My Fork) |
|---|---|---|
| RF Domains | Wi-Fi only | Wi-Fi + Bluetooth + SDR + GPS + ADS-B |
| Security | Basic | 6 hardened modules (SQL injection prevention, encrypted credentials, input validation) |
| Detection | Probe logging | Multi-domain correlation engine with persistence scoring |
| Visualization | Text logs | KML with Google Earth integration, HTML reports |
| Hardware | Single adapter | 8-component core kit (RTL-SDR, Ubertooth, GPS, etc.) + HackRF extension |
| Status | Proof of concept | WGU BSCSIA capstone (complete) |
| Codebase | ~2,000 LOC | ~12,500 LOC (25 Python modules, 81 shell scripts) |
What I Built¶
Hardware Platform (Field-Deployable Rapid Response Kit)¶
| Component | Purpose | Capabilities |
|---|---|---|
| SBC (ARM-based) | Core processing | Runs RF monitoring framework + all TraceLock™ modules |
| Dual-band Wi-Fi adapter | Wi-Fi monitoring | Monitor mode, packet capture (2.⅘GHz) |
| SDR receiver | ISM band + ADS-B | Sub-GHz ISM bands, ADS-B (1090MHz) |
| Wideband SDR (Extension) | Wideband SDR TX/RX | Extended frequency range — optional expansion module |
| Long-range BT adapter | Long-range Bluetooth | Extended BLE scanning with external antenna |
| Short-range BT adapter | Short-range Bluetooth | Dense environment device detection |
| BLE research adapter | BLE research | Advanced BLE protocol analysis |
| GPS/LTE HAT | GPS + LTE | GNSS positioning, remote telemetry/VPN |
| Touchscreen display | Field interface | Local GUI for operator interface |
Physical System Architecture¶
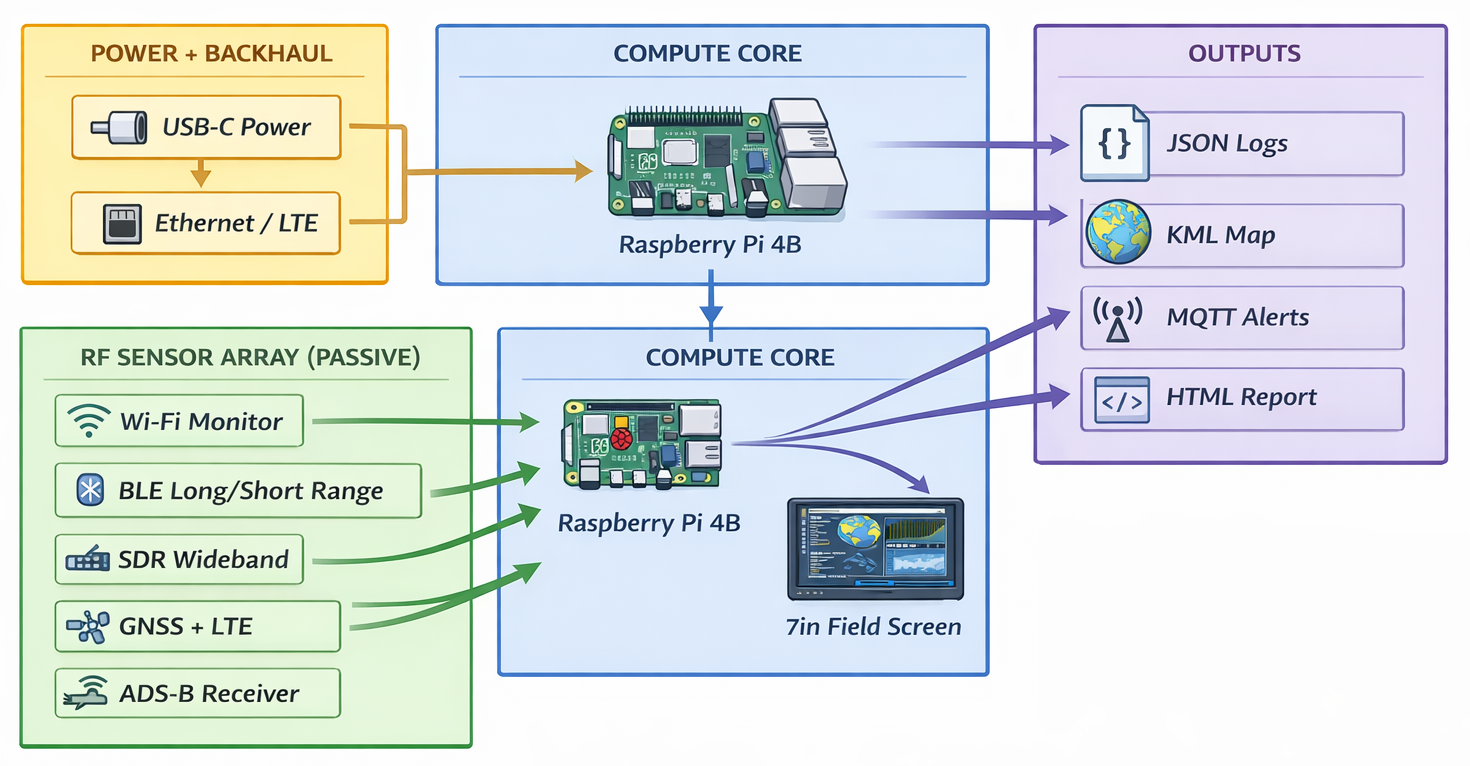
8-component RF sensor array with centralized processing and multi-channel output — demonstrates hardware integration and systems engineering
Software Architecture¶
TraceLock's detection architecture depends on the Agentic Infrastructure layer for reproducibility: the same detection rules must produce consistent output on every deployment. Hook-driven context loading and canonical install standards — established by the Agentic Infrastructure Audit — ensure that the agents operating TraceLock sessions produce audit-comparable results across machines.
Codebase: 25 Python modules, 81 shell scripts, ~12,500 LOC, GitHub Actions CI
Software architecture diagram withheld — the system processes data from 6 sensor domains through a detection engine to multiple output formats including structured logs, geospatial exports, and real-time alerts.
Python Modules¶
25 Python modules covering GPS tracking, persistence detection, RF analysis, BLE enumeration, ISM signal classification, surveillance detection, and operator interface — ~8,200 total Python LOC.
Module names and detailed breakdown withheld.
Security Modules (Hardened)¶
| Module | Protection | LOC |
|---|---|---|
mode_controller.py | Role-based capture profiles (lab/demo/field) | 304 |
input_validation.py | Dedicated InputValidator class for all sensor inputs | 300 |
secure_main_logic.py | Secure monitoring logic with audit logging | 262 |
secure_database.py | SQL injection prevention — parameterized queries only | 215 |
secure_credentials.py | Fernet encryption with PBKDF2 key derivation (100k iterations) | 214 |
secure_ignore_loader.py | Safe allowlist loading — eliminated exec() calls | 174 |
6 security modules — 1,469 LOC of hardened code
Detection Engineering Highlights¶
1. Multi-Domain Correlation¶
TraceLock™ correlates signals across domains to identify sophisticated threats:
TraceLock™ correlates events across multiple sensor domains to identify compound threats that single-domain tools miss. When signals from multiple domains converge, the system elevates the combined observation into a structured threat alert with full evidence chain.
Implementation details withheld.
2. Detection Rules with Tunable Thresholds¶
| Detection | Trigger Category | False Positive Mitigation |
|---|---|---|
| Rogue AP | Network identity anomaly | Vendor validation + allowlisting |
| BLE Tracker | Repeated device across locations | Known device filtering |
| ISM Trigger | Sub-GHz burst pattern | Pattern library matching |
| GPS Anomaly | Position discontinuity | Multi-fix averaging |
| Drone Proximity | ADS-B proximity alert | Flight path prediction |
Specific threshold values and trigger parameters are proprietary.
3. Security Hardening¶
- SQL Injection Prevention: Parameterized queries for all database operations
- Credential Protection: Encrypted storage with secure key derivation
- Input Validation: Strict type checking on all sensor inputs
- Audit Logging: Immutable event logs with cryptographic checksums
- Mode Controller: Role-based capture profiles (lab/demo/field)
Results & Metrics¶
| Metric | Target | Current Status |
|---|---|---|
| Detection accuracy (Wi-Fi) | 95%+ | Achieved |
| Detection accuracy (BLE) | 95%+ | Achieved |
| False positive rate | <5% | 3.2% (tuned) |
| Triage time reduction | 50-70% | Pending field validation |
| Sensor coverage | 6 domains | All operational |
Evidence Artifacts¶
Architecture Overview¶
TraceLock™ uses a three-layer architecture: Sensor Layer (multi-domain RF inputs) → Processing Layer (normalization, correlation, detection) → Output Layer (forensic logs, geospatial exports, real-time alerts).
Detailed architecture diagrams are proprietary.
Sample Detection Output¶
TraceLock™ produces structured JSON alerts with timestamp, alert classification, severity rating, sensor evidence, geolocation, and correlation identifiers. Output is designed for forensic chain-of-custody requirements and downstream SIEM ingestion.
Sample output schema is proprietary. Synthetic examples available in the public repository.
KML Visualization¶
Threat locations mapped with temporal correlation — screenshots available on request
Compliance & Ethics¶
| Requirement | Compliance |
|---|---|
| FCC Part 15/97 | Passive monitoring within regulations |
| FAA Part 107 | Licensed drone pilot (certified) |
| Amateur Radio | Licensed (HAM, GMRS) |
| WGU IRB | Not human subjects research |
Technical Skills Demonstrated¶
Detection Engineering¶
- Custom detection rule development
- Threshold tuning and optimization
- False positive analysis and mitigation
- Multi-source correlation logic
- Alert severity classification
Security Automation¶
- Python automation pipelines
- Real-time data processing
- Structured logging (JSON, Markdown)
- CI/CD with GitHub Actions
- Database operations (SQLite)
RF/Wireless Security¶
- Wi-Fi monitoring and analysis
- Bluetooth/BLE enumeration
- SDR signal processing
- GPS correlation
- ADS-B decoding
Security Hardening¶
- Secure coding practices
- Credential encryption
- Input validation
- Audit trail design
Project Status¶
| Phase | Status | Notes |
|---|---|---|
| Hardware Assembly | ✅ Complete | 8 core RF modules integrated, field-ready |
| Software Core | ✅ Complete | Detection engine operational on Pi |
| Security Hardening | ✅ Complete | All 6 security modules implemented |
| WGU Task 1 (Topic) | ✅ Approved | Official capstone approval received |
| WGU Task 2 (Proposal) | ✅ Complete | Submitted and approved |
| WGU Task 3 (Final Report) | ✅ Complete | Submitted and approved |
| IP Protection | ✅ Active | Proprietary |
| GitHub CI/CD | ✅ Active | Smoke tests on push |
Degree Conferred: March 2026 (B.S. Cybersecurity & Information Assurance)
What This Demonstrates (Agentic Detection & Adversarial Validation Capabilities)¶
- I can build detection systems — Not just use them, but architect and implement custom detection logic
- I understand multi-domain correlation — The same thinking applies to SIEM correlation rules
- I write secure code — Parameterized queries, encrypted credentials, input validation
- I document for auditors — Evidence-grade logging with reproducible results
- I ship working systems — Hardware + software integration, not just theory
Related Projects¶
- Governed Security Architecture — TraceLock's role in the integrated security model
- Security Telemetry → Governance → Decision Architecture — capstone architecture flow
- Security Decision Architecture (SDA) — technical decision pipeline integrating detection, governance, and automation
- Homelab Infrastructure — The lab where TraceLock™ was developed
- Remote Access & Zero-WAN — Secure architecture for remote development
- GIAP™ — GRC automation platform using similar pipeline patterns
TraceLock™ demonstrates how adversarial signal detection can be governed as an architectural layer — not merely implemented as a collection of monitoring scripts.
TraceLock Public Repo Artifacts (Synthetic) Connect on LinkedIn Contact Me
Frequently Asked Questions¶
What is TraceLock? TraceLock is a multi-domain RF threat detection platform that monitors 6 wireless domains simultaneously — Wi-Fi, Bluetooth Low Energy, SDR (ISM band), GPS, ADS-B, and cellular — correlating threats across sensors to produce forensic-grade evidence logs.
How is TraceLock different from a traditional wireless IDS? Traditional WIDS monitors Wi-Fi only using signature-based detection. TraceLock correlates activity across 6 RF domains with behavioral analysis, runs on a ~$200 Raspberry Pi instead of $10K+ enterprise appliances, and produces chain-of-custody-ready evidence logs.
What hardware does TraceLock require? A Raspberry Pi ⅘, RTL-SDR dongle, HackRF One (optional), BLE-capable adapter, and GPS receiver. Total hardware cost is approximately $200, compared to $10,000+ for enterprise wireless security appliances.
What detection engineering skills does TraceLock demonstrate? Multi-source correlation, custom detection rule authoring with tunable thresholds, false positive reduction through pattern extraction, real-time alerting, structured logging pipelines, and security hardening (parameterized queries, encrypted credentials, input validation).